How Digital Forensic Services Boost Data Security Measures?

-
Content
- Introduction
- Detection of Security Breaches
- Incident Response and Mitigation
- Preservation of Digital Evidence
- Analysis and Investigation
- Conclusion
-
Content
- Introduction
- Detection of Security Breaches
- Incident Response and Mitigation
- Preservation of Digital Evidence
- Analysis and Investigation
- Conclusion
Introduction
The protection of data is a critical issue for both organizations and individuals in the swiftly changing digital environment of the present day. Digital forensic services have become an indispensable safeguard against the escalating intricacy of cyber threats. These services provide all-encompassing remedies to ensure that sensitive data remains undetected and protected against cyber-attacks, unauthorized intrusions, and other forms of digital misconduct. These services encompass a wide array of techniques and methodologies aimed at identifying, preserving, analyzing, and presenting data in a manner that is legally admissible. Digital forensics companies leverage advanced digital forensics tools and solutions to meticulously dissect cyber incidents, ensuring an effective incident response, and thereby, enhancing overall data security measures. By employing digital forensics expert, these services not only aid in unraveling the intricacies of cyber crimes but also play a vital role in fortifying the cyber security posture of entities. It is impossible to exaggerate the importance of digital forensic services in the modern world, they are critical to maintaining the integrity of digital assets and protecting digital evidence, which in turn guarantees the continuity and resilience of operations in the face of digital challenges.
Detection of Security Breaches
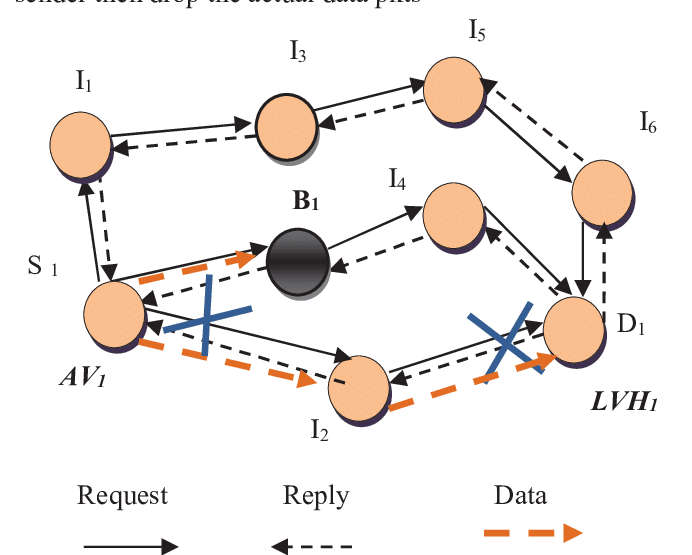
Identifying security breaches in the digital realm requires a sophisticated blend of techniques and expertise, foundational to the practice of digital forensic services. This multifaceted approach is critical for dissecting the often-complex web of cyber incidents, enabling organizations to respond effectively and secure their digital environments.
1. Evidence Collection
The first stage of identifying security breaches is collecting evidence with great care. Experts in digital forensics collect data from compromised systems using a range of digital forensics instruments. This include taking screenshots, safeguarding disk images, and recording information from volatile memory. These actions collectively provide the foundation for further forensic investigation.
2. Data Analysis
The focus switches to thorough data analysis after the gathering of evidence. At this phase, the gathered data is combed through to find any anomalies or trends that could point to a security breach. In order to piece together the sequence of events leading up to the incident, techniques like chronology analysis, hash analysis, and keyword searches are essential.
3. Events Reconstruction
It is essential to reconstruct the sequence of events in order to comprehend how a breach transpired. This requires the delineation of the attacker’s activities within the network, commencing with their initial intrusion and concluding with the implementation of unauthorized tasks. By facilitating the reconstruction of the breach’s timeline, digital forensics solutions provide investigators with invaluable information regarding the exploited vulnerabilities and the magnitude of the damage.
4. Attacker Identification
Analyzing digital footprints left behind is a complex part of digital forensics investigation that involves identifying the attackers. IP addresses, user account activity, and behavioral patterns that can point to the attack’s origin are examples of this.
5. Impact Assessment
Lastly, it’s critical to evaluate the effects of a security breach. This entails figuring out how much data has been compromised, which systems have been impacted, and what kind of consequences the firm could face. Forensic analysis and digital evidence are essential in determining the extent of the breach and directing the recovery effort.
Incorporating these techniques, digital forensic services stand at the forefront of cyber security, offering indispensable tools in the detection and analysis of security breaches, thereby enhancing data security measures in an increasingly vulnerable digital landscape.
Incident Response and Mitigation
In the domain of cyber security, the rapidity and efficiency of incident response and mitigation underscore the invaluable role of digital forensic services. These services, including computer forensics services, are instrumental in diagnosing the extent of a cyber incident, facilitating a swift and informed response crucial in minimizing potential damages and restoring operations.
1. Aiding Incident Response through Digital Forensics
Digital forensic services provide a structured approach to incident response, ensuring that every step, from the initial detection to the final resolution, is underpinned by detailed forensic analysis. This begins with the immediate preservation of digital evidence to prevent data tampering or loss. Forensic experts utilize specialized digital forensics tools to analyze this evidence, enabling them to identify the nature of the breach, the techniques employed by the attackers, and the scope of the impacted systems. Such insights are vital for tailoring the incident response strategy to effectively address the specific challenges posed by the breach.
2. Timely Response and Mitigation
Reduction of security event impact is mostly dependent on promptness of reaction. The immediate and long-term effects of a cyber attack can be considerably reduced by acting swiftly and decisively. In order to avoid more unauthorized access, this entails stopping the breach, eliminating the danger from the network, and starting the recovery procedures to restore the affected services and data. Using digital forensics solutions, which provide the tools to swiftly collect and examine incident-related data, is essential to executing this prompt reaction.
3. SalvationDATA’s Role in Incident Response
SalvationDATA, with its comprehensive suite of forensics cyber security tools, including advanced DFIR (Digital Forensics and Incident Response) capabilities, aids organizations in swiftly identifying the specifics of a breach, thereby accelerating the response process. Their sophisticated computer forensics services and DFIR tools enable detailed analysis necessary for understanding the attack vector and mitigating further risks.
4. Additional Company Examples
Other entities, such as prominent cyber security firms and digital forensics solutions providers, further exemplify the critical support role in incident response. Companies like CrowdStrike and FireEye offer advanced incident response services, leveraging their dfir tools and expertise to assist organizations in navigating the aftermath of security breaches. Their capabilities in rapid threat detection and response are instrumental in minimizing downtime and financial losses, showcasing the vital contribution of digital forensic services in contemporary cyber security strategies.
To sum up, successful cyber security management requires the incorporation of digital forensic services into incident response frameworks. These services enable organizations to remain resilient in the face of a constantly changing threat landscape by enabling the swift identification, analysis, and mitigation of cyber threats. This improves the overall security posture and guarantees the protection of vital digital evidence and assets.
Preservation of Digital Evidence
The preservation of digital evidence is a cornerstone of digital forensic services, ensuring that information critical to legal and regulatory proceedings remains intact, authentic, and credible. This practice is not just about retaining data but about maintaining its integrity and reliability for its potential use in a court of law or for compliance purposes. The importance of such preservation cannot be overstated, as it underpins the ability of organizations to defend or prosecute in cyber-related cases, ensuring that justice can be served and regulatory requirements are met.
Ensuring the Integrity and Admissibility of Digital Evidence
1. Adherence to Guidelines
Digital evidence preservation starts with rigorous adherence to forensic standards and procedures. By offering forensic professionals an organized strategy for managing evidence, these frameworks make sure that their job is done consistently and methodically. Experts in digital forensics ensure that the evidence is preserved in its original form so that it may be examined legally by adhering to these criteria.
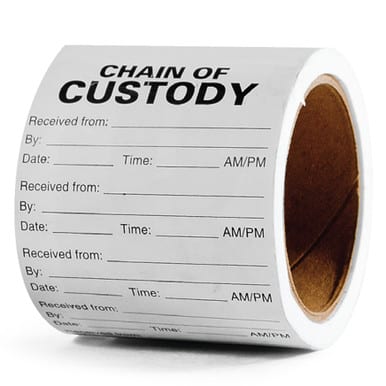
2. Chain of Custody
As it records all interactions with the evidence from its acquisition to its court presentation, the chain of custody is an essential component of evidence preservation. In order to support the admissibility of the evidence in court, it is imperative that the careful record-keeping be used to show the evidence’s ongoing security and management. All procedural actions made with the digital evidence are visible and accountable when the chain of custody is well managed.
1. Verification of Legal Authority
Verifying legal authorization is another step in the preservation of digital evidence, ensuring that data collection and analysis are carried out in compliance with the law. This involves securing any warrants or authorization needed in order to access and inspect digital assets. Maintaining the rights of people concerned and making sure that the evidence gathered is regarded as valid and admissible in a court of law depend heavily on this kind of attentiveness.
2. Preservation Techniques
Advanced preservation procedures are employed by digital forensic services to safeguard evidence against unintentional or purposeful modification, deterioration, or loss. These methods involve assuring safe storage settings, utilizing write-blockers to prevent data tampering, and producing forensic photographs of digital storage devices. These procedures are necessary to keep the evidence in perfect shape so that it may be analyzed and possibly even tested in court.
3. Scientific Validity
Last but not least, a key component of the evidence’s preservation is its scientific legitimacy. This means applying established and approved digital forensics techniques and technologies that have been validated within the forensic community. The evidence’s value and reliability in the legal system are strengthened by the implementation of scientifically sound procedures, which guarantee that the evidence can resist severe legal challenges.
In short, the meticulous preservation of digital evidence through these forensic procedures not only ensures its integrity and admissibility but also strengthens the overall efficacy of digital forensic services in legal and regulatory contexts. By adhering to stringent standards and practices, forensic professionals safeguard the foundational pillars of justice and regulatory compliance in the digital age.
Analysis and Investigation
The forensic analysis process is a pivotal component of digital forensic services, offering a systematic approach to dissecting security incidents. This in-depth investigation enables experts to unearth the root cause of breaches, understand the methods used by attackers, and identify compromised data. Through a meticulous examination of digital evidence, forensic professionals can piece together the actions that led to the incident, providing crucial insights that inform the development of more robust security measures.
Techniques in Forensic Analysis
1. Malware Analysis
Understanding the tools that attackers utilize is made possible through the use of malware analysis. Digital forensics specialists can identify malicious software’s functioning, source, and any effects on impacted computers by analyzing it. This study helps strengthen defenses against similar assaults in the future in addition to assisting in the mitigation of the current danger. Experts can reverse-engineer malware using digital forensics tools, providing information on the attacker’s goals and techniques.
2. Memory Forensics
Finding out what an attacker is doing within a system is made possible in large part by memory forensics. Using this method, information about active processes, open connections, and user activity that is not visible in static files may be retrieved by examining volatile data in a system’s RAM. Memory forensics provides investigators with crucial information for a comprehensive investigation by enabling them to find signs of malware execution, illegal access, and other intrusion indications.
3. Network Traffic Analysis
Analyzing network data is crucial to determining the extent and kind of a security compromise. Forensic analysts can determine which data was exfiltrated, follow the path of an attack, and determine the origin of an attack by looking at data packets that are being sent to and from a hacked system. This method offers a thorough understanding of the attacker’s activities and tactics, making it easier to respond with specific security measures to safeguard the network and stop similar attacks in the future.
In summary, the forensic analysis process encompasses a suite of sophisticated techniques, including malware analysis, memory forensics, and network traffic analysis. Each plays a vital role in the thorough investigation of security incidents, underscoring the indispensable value of digital forensic services in today’s cybersecurity landscape.
Conclusion
Digital forensic services play a crucial role in the field of cyber security. These services shed light on the nuances of security breaches through painstaking evidence collecting, in-depth analysis, and thorough investigation. These crucial insights help shape efficient incident response and mitigation plans. Digital forensics serves as a defense against the constantly changing risks in the digital world, from the early identification of illicit activity to the preservation of digital evidence for legal processes. Cyber incident analysis relies heavily on techniques like malware analysis, memory forensics, and network traffic analysis, which provide insight into the strategies and objectives of attackers. In addition, the enforcement of stringent protocols and norms guarantees the credibility and validity of data, strengthening the legal and administrative structures that support our technologically advanced society. Digital forensic services are critical to improving data security measures as we negotiate the complexity of the digital era. They are the first line of defense for safeguarding digital assets and maintaining cyber resilience.