Due to the influence of movies and popular culture, people often get inaccurate ideas about this line of work and the overall digital forensics process. But that’s okay! After all, someone who’s not from the inner circle may have a hard time understanding how digital forensics investigations really work.
In fiction, the entire digital investigation process tends to get romanticized, and many hardships law enforcement agencies have to endure often get portrayed in a sugar-coated manner. In turn, this can lead to many people internalizing certain falsehoods about how things play out in reality.
Examples include “magically” enhancing or upscaling blurry photos and video footage, analyzing tissue samples within a moment’s notice, and blazing through complex passwords and encryption like it’s nothing.
Below, we’re about to give you the good, the bad, and the ugly on everything you ever wanted to know about the true nature of digital forensics investigations:







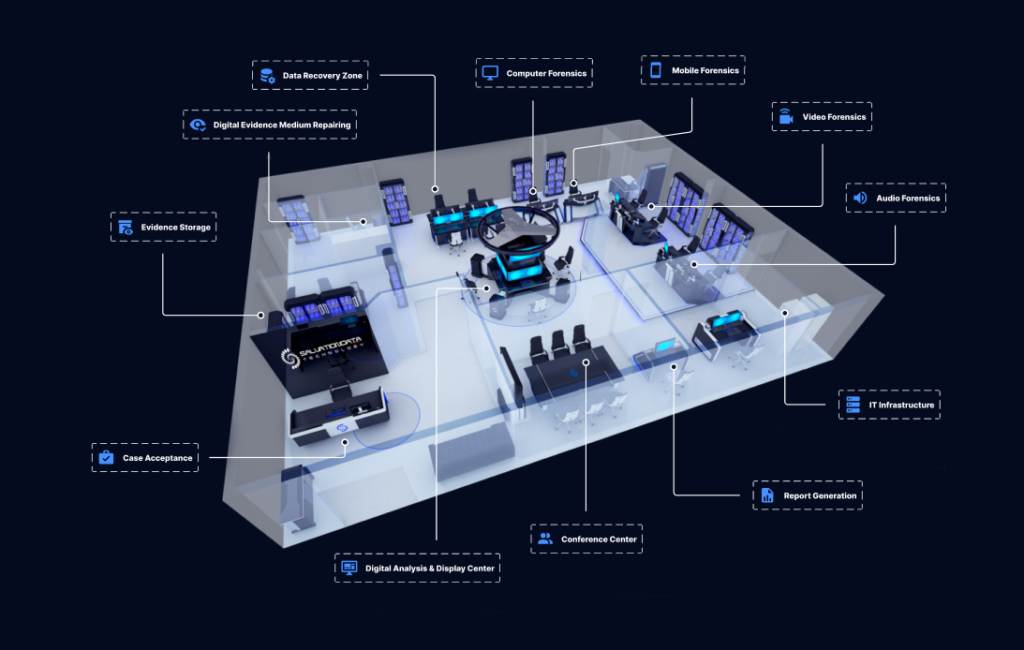 A reputable law enforcement organization needs a professional one-stop digital forensics software solution like SalvationDATA’s
A reputable law enforcement organization needs a professional one-stop digital forensics software solution like SalvationDATA’s 
