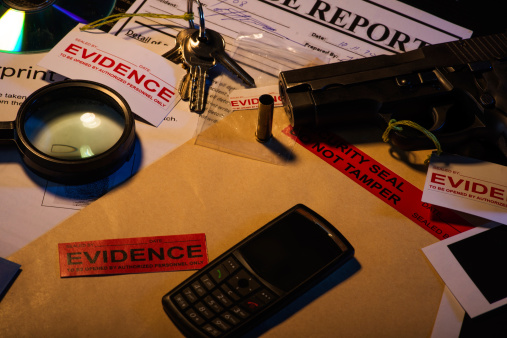
Our mobile devices are not just for calls and SMS anymore; they are the catalogues of our actions and interests. Personal devices like smartphones and tablets are so closely integrated into our lives that they retain a record of the things that even we forget, which is said that our devices know us better than even we do.
Under the circumstance, it means even more in mobile forensics.