In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
Author: SalvationDATA Digital Forensics Team
Key Steps in Malware Analysis for Digital Forensics Investigations
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
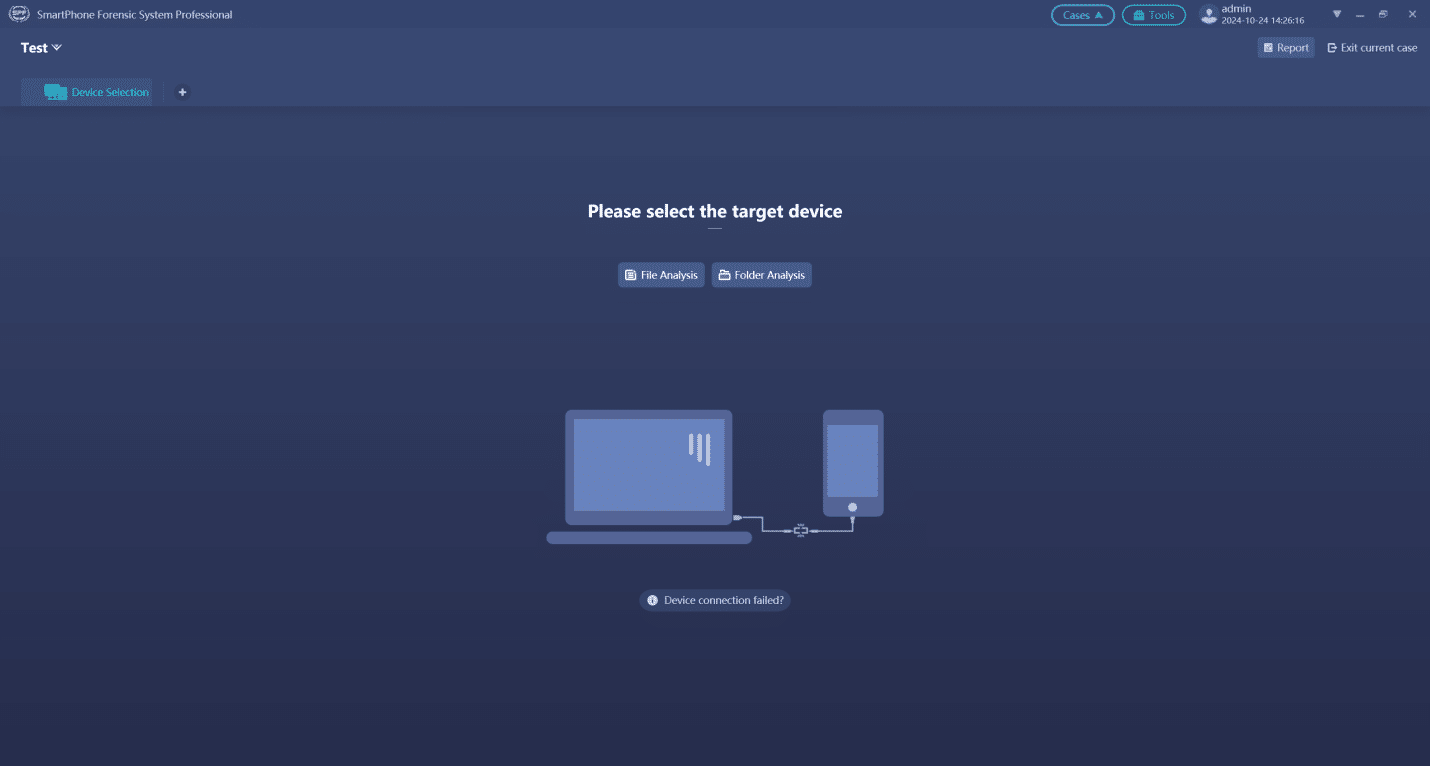
3 Steps to Identify a Mobile Phone When Disconnected.
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
Essential Forensic Imaging Tools for Digital Investigations
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
6 Computer Forensics Skills Every Investigator should know
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
Top 5 Data Carving Tools for Recovering Lost Files
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
File Carving vs. Metadata Recovery: What’s the Difference?
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
Is Envista Forensics Worth it? A Look at Their Tools and Techniques
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
Is WhatsApp Safe? A Digital Forensics Perspective
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.
Top 5 Database Encryption Techniques for Businesses
In the area of digital forensics, which is changing very quickly, keeping digital data safe is very important. MD5 and SHA1 were once thought to be the best security methods for forensic investigations, but now they are being looked at more closely because they are weak. Even though worries are rising, they are still used to make sure that proof is real in digital forensics. As technology changes, the question comes up: Are these hash numbers no longer useful or necessary? This piece talks about how MD5 and SHA1 are used in digital forensics. It talks about their pros and cons and the current discussion about their future in cybersecurity.