What’s privacy coin?
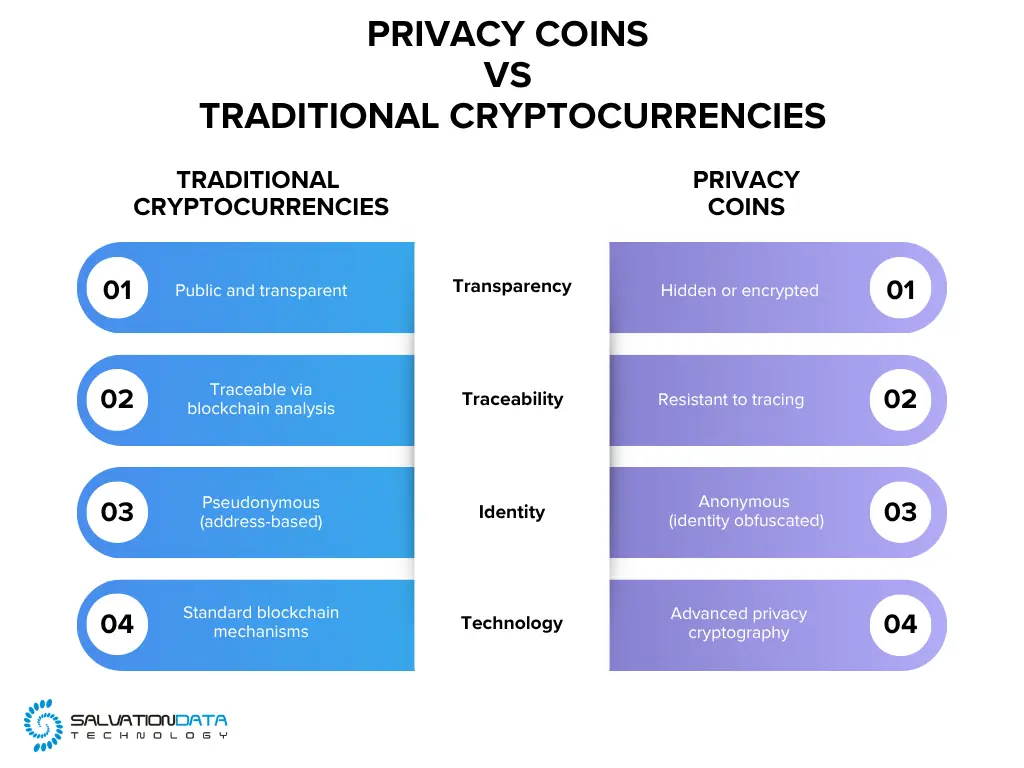
Privacy coins are a category of cryptocurrencies specifically designed to enhance transaction privacy and user anonymity. Unlike standard cryptocurrencies, which often record transaction details on publicly accessible blockchains, privacy coins employ advanced cryptographic techniques to obscure key data such as sender and receiver identities, wallet addresses, and transaction amounts.
Common examples include Monero (XMR), Zcash (ZEC), and Dash (DASH). Findings from organizations such as Chainalysis and Europol indicate that these privacy features can significantly complicate traditional blockchain analysis.